A Story emerges
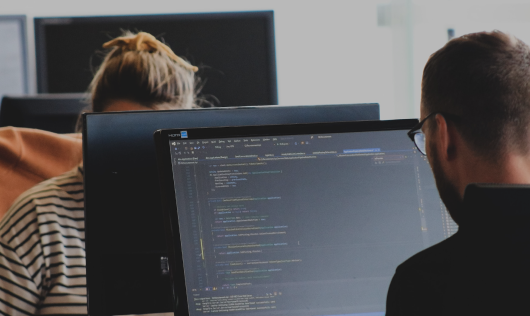
The vulnerability is the endpoint of a long journey. First we trace the vulnerability to its source code fix. Then we mine the repository to find the Vulnerability Contributing Commit (VCC). Then we automatically construct a timeline, then tag. A curator then comes along and corrects the data, telling the broader story of the vulnerability.
With this methodology, what appears to be a "simple coding mistake" becomes a unique narrative. Reality is messy, tedious, and nuanced.
Our philosophy is to always provide more context and let the story tell itself
 The Vulnerability History Project
The Vulnerability History Project